Cyber correspondent
 BBC
BBCVirtually every day, my telephone pings with messages from hackers of all stripes.
The great, the dangerous, the not-so-sure.
I have been reporting on cyber safety for greater than a decade, so I do know that lots of them like to speak about their hacks, findings and escapades.
About 99% of those conversations keep firmly locked in my chat logs and do not result in information tales. However a latest ping was unimaginable to disregard.
“Hey. That is Joe Tidy from the BBC reporting on this Co-op information, appropriate?” the hackers messaged me on Telegram.
“We now have some information for you,” they teased.
After I cautiously requested what this was, the individuals behind the Telegram account – which had no title or profile image – gave me the within monitor on what they claimed to have completed to M&S and the Co-op, in cyber assaults that triggered mass disruption.
By way of messages back-and-forth over the subsequent 5 hours, it turned clear to me that these obvious hackers had been fluent English audio system and though they claimed be messengers, it was apparent they had been carefully linked to – if not intimately concerned in – the M&S and Co-op hacks.
They shared proof proving that they’d stolen an enormous quantity of personal buyer and worker data.
I checked out a pattern of the info they’d given me – after which securely deleted it.
Messages that confirmed suspicions
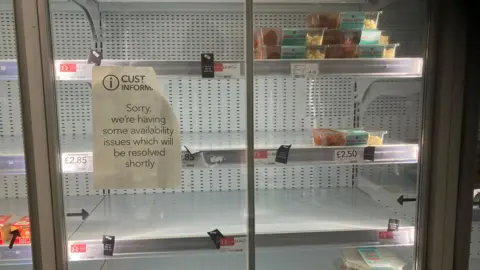
They had been clearly pissed off that Co-op wasn’t giving in to their ransom calls for however would not say how a lot cash in Bitcoin they had been demanding of the retailer in change for the promise that they would not promote or give away the stolen information.
After a dialog with the BBC’s Editorial Coverage crew, we determined that it was within the public curiosity to report that they’d supplied us with proof proving that they had been answerable for the hack.
I shortly contacted the press crew on the Co-op for remark, and inside minutes the agency, who had initially downplayed the hack, admitted to workers, clients and the inventory market concerning the vital information breach.
A lot later, the hackers despatched me a protracted offended and offensive letter about Co-op’s response to their hack and subsequent extortion, which revealed that the retailer narrowly dodged a extra extreme hack by intervening within the chaotic minutes after its pc systems were infiltrated. The letter and dialog with the hackers confirmed what consultants within the cyber safety world had been saying since this wave of assaults on retailers started – the hackers had been from a cyber crime service known as DragonForce.
Who’re DragonForce, you is perhaps asking? Primarily based on our conversations with the hackers and wider data, we have now some clues.
DragonForce affords cyber prison associates varied companies on their darknet website in change for a 20% minimize of any ransoms collected. Anybody can join and use their malicious software program to scramble a sufferer’s information or use their darknet web site for his or her public extortion.
This has develop into the norm in organised cyber crime; it is often known as ransomware-as-a-service.
Probably the most notorious of latest instances has been a service known as LockBit, however that is all however defunct now partly as a result of it was cracked by the police final yr.
Following the dismantling of such teams, an influence vacuum has emerged. Cue a tussle for dominance on this underground world, resulting in some rival teams innovating their choices.
Energy wrestle ensues
DragonForce lately rebranded itself as a cartel providing much more choices to hackers together with 24/7 buyer assist, for instance.
The group had been promoting its wider providing since not less than early 2024 and has been actively concentrating on organisations since 2023, in response to cyber consultants like Hannah Baumgaertner, Head of Analysis at Silobeaker, a cyber threat safety firm.
“DragonForce’s newest mannequin contains options resembling administration and consumer panels, encryption and ransomware negotiation instruments, and extra,” Ms Baumgaertner stated.
As a stark illustration of the power-struggle, DragonForce’s darknet web site was lately hacked and defaced by a rival gang known as RansomHub, earlier than re-emerging a few week in the past.
“Behind the scenes of the ransomware ecosystem there appears to be some jostling – that is perhaps for prime ‘chief’ place or simply to disrupt different teams with the intention to take extra of the sufferer share,” stated Aiden Sinnott, senior menace researcher from the cyber safety firm Secureworks.
Who’s pulling the strings?
DragonForce’s prolific modus operandi is to publish about its victims, because it has completed 168 instances since December 2024 – a London accountancy agency, an Illinois metal maker, an Egyptian funding agency are all included. But to this point, DragonForce has remained silent concerning the retail assaults.
Usually radio silence about assaults signifies {that a} sufferer organisation has paid the hackers to maintain quiet. As neither DragonForce, Co-op nor M&S have commented on this level, we do not know what is perhaps occurring behind the scenes.
Establishing who the persons are behind DragonForce is hard, and it is not recognized the place they’re positioned. After I requested their Telegram account about this, I did not get a solution. Though the hackers did not inform me explicitly that they had been behind the latest hacks on M&S and Harrods, they confirmed a report in Bloomberg that spelt it out.
In fact, they’re criminals and may very well be mendacity.
Some researchers say DragonForce are primarily based in Malaysia, whereas others say Russia, the place many of those teams are considered positioned. We do know that DragonForce has no particular targets or agenda aside from being profitable.
And if DragonForce is simply the service for different criminals to make use of – who’s pulling the strings and selecting to assault UK retailers?
Within the early levels of the M&S hack, unknown sources informed cyber information website Bleeping Pc that proof is pointing to a unfastened collective of cyber criminals often known as Scattered Spider – however this has but to be confirmed by the police.
Scattered Spider is just not actually a bunch within the regular sense of the phrase. It is extra of a neighborhood which organises throughout websites like Discord, Telegram and boards – therefore the outline “scattered” which was given to them by cyber safety researchers at CrowdStrike.
They’re recognized to be English-speaking and possibly within the UK and the US and younger – in some instances youngsters. We all know this from researchers and former arrests. In November the US charged 5 males and boys of their twenties and youths for alleged Scattered Spider exercise. Considered one of them is 22-year-old Scottish man Tyler Buchanan, who has not made a plea, and the remaining are US primarily based.
Crackdowns by police appear to have had little impact on the hackers’ willpower, although. On Thursday, Google’s cyber safety division issued warnings that it was beginning to see Scattered Spider-like assaults on US retailers now too.
As for the hackers I spoke to on Telegram, they declined to reply whether or not or not they had been Scattered Spider. “We can’t reply that query” is all they stated.
Maybe in a nod to the immaturity and attention-seeking nature of the hackers, two of them stated they wished to be often known as “Raymond Reddington” and “Dembe Zuma” after characters from US crime thriller The Blacklist which includes a wished prison serving to police take down different criminals on a blacklist.
In a message to me, they boasted: “We’re placing UK retailers on the Blacklist.”